There are many reasons to harden your VPS. The best practices for VPS security involve learning the settings, steps, and options that are needed to keep your server secure. You will also find yourself continually researching and updating your knowledge and software tools to keep your security up-to-date.
Server security depends on everyone who interacts with the server. Due to this, it is important to keep in mind that all administrators working on the VPS are responsible for its security.
This article will explain how to secure a VPS in 24 different ways. Some of these items will focus on the server, whereas others will apply to your operating system, application, website software, and secure VPS hosting.
- 1. Use a Firewall – APF and CSF
- 2. Close Unnecessary Ports
- 3. Change Default Listening SSH Port
- 4. Malware AV Scanner
- 5. Intrusion Detection Software
- 6. Brute Force Security
- 7. Use SSH Keys
- 8. Use SFTP Instead of FTP
- 9. Spam Filtering
- 10. Disable IPV6
- 11. Disable Root Logins
- 12. Limit User Access
- 13. Set up a Disaster Recovery Plan – Backups
- 14. Keep Everything Up-to-date
- 15. Monitor Server Logs
- 16. Implement Strong Password Policy
- 17. PCI DSS Compliance
- 18. Use SSL Certificates
- 19. Security HTTP Headers and Subresource Integrity (SRI)
- 20. PHP Versioning
- 21. Disk Partitioning
- 22. Specific Security for your Operating System
- 23. Training and Research VPS Security
- 24. Find a Secure Hosting Service
1. Use a Firewall – APF and CSF
There are many types of firewalls that you can use for hardening VPS security. It is important that you enable or configure one as soon as you have the server running. Firewalls can help detect and prevent brute-force login attempts, port scans, and other network-based attacks within your web server traffic.
APF – Advanced Policy Firewall
Advanced Policy Firewall (APF) should be installed on your server by default.
APF allows for easy management of your iptables firewall rules for things such as opening ports in your firewall.
Here are some example commands:
Add IP to allowed hosts:apf -a 123.123.123.123 “Home IP”Block IP from server:
apf -d 123.123.123.123 “Hitting login.php again and again”Unblock a blocked IP:
apf -u 123.123.123.123Block IP ranges:
apf -d 123.123.123.123/24 Not recommendedRecommended way to block IP range from accessing port 80
vi /etc/apf/deny_hosts.rules d=80:s=123.123.123.123/24
CSF – ConfigServer Firewall
ConfigServer Firewall (CSF) also allows for easy iptables management. CSF is more recent, and more robust, than APF. It allows for temporary blocking of IPs and has both SYN flood protection to help against SYN flood DDoS attacks, as well as LFD which is the built-in module that deals with brute-force login protection.
Here are some example commands:
Allow an IP:csf -a 123.123.123.123Temp allow an IP:
csf -ta 123.123.123.123 15s (s – seconds / h – hours / m – minutes / d – day)Block an IP:
csf -d 123.123.123.123Temp block an IP
csf -td 123.123.123.123 15s (s – seconds / h – hours / m – minutes / d – day)Unblock a permanent blocked IP:
csf -dr 123.123.123.123Unblock a temporary blocked IP:
csf -tr 123.123.123.123List temporary blocked IPs and durations:
csf -tRemove all temporary IP blocks:
csf -tfLog all SYN packets from an IP
csf -w 123.123.123.123
For more details on what you can do with these firewalls, please see Server Security Best Practices.
2. Close Unnecessary Ports
You should close unnecessary ports in order to prevent their use by unauthorized traffic. In order to see the open ports on your server, you can run the netstat command. This will reveal all the open network ports and their associated services.
netstat
You can also use the Nmap command in order to discover hosts and services.
nmap domain.com
Some of nmap’s options include:
- Provide information on targets, including reverse DNS names, device types, and MAC addresses
- Host discovery – identifying hosts on a network
- Port scanning – identifying open ports
- OS detection – finding the operating system and hardware info of network devices
Here is an example of the results from an Nmap scan:
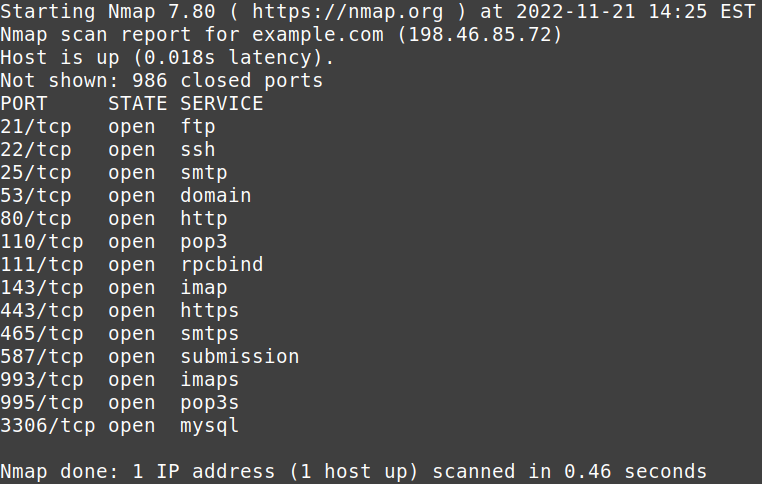
To learn more about closing ports with APF, please see Close Open Ports for PCI Compliance.
3. Change Default SSH Listening Port
Port 22 is the default SSH port and it’s open by default. Changing your server SSH port can protect you from a lot of less sophisticated attacks. If you’re a cPanel administrator with root WebHost Manager (WHM) access, you should disable SSH access for cPanel accounts that don’t need it.
Below are the basic steps, but to learn more about changing the port, please see How to Change Your Server SSH Port.
Changing SSH Ports
- Connect to your server via SSH as the root user.
- Edit your SSH config file in the following location:
/etc/ssh/sshd_config
- Find the line containing #Port 22 and then remove the hashtag and replace 22 with the port you want to use.
4. Malware AV Scanner
Malware is continually evolving and so must the systems that are used to monitor and remove it from your server. Server security is not perfect. Malicious traffic can get through.
So, it’s important that anti-malware software is installed, regularly updated, and used. Anti-malware software should be considered essential and a required part of the steps to harden VPS security for your hosting account.
If you are on a managed hosting server, chances are that your hosting team already utilizes software for this purpose. They may not tell you their exact software (for security purposes), but you should inquire to make sure that they do regularly scan your server.
ClamAV and Maldet are two open-source applications that can scan your server and identify potential threats. There are many other malware scanners available with many requiring payment. Here’s a list of free antivirus/malware software:
- ClamTk – lightweight, quick, antivirus scanner; provides a graphic interface
- Comodo Anti-virus For Linux (CAVL) – features include antivirus scanning, anti-spam system, automatic updates, and scan scheduling
- Sophos for Linux – antivirus/malware scanning with scheduling, low impact on system resources
- ChkrootKit – checks system binaries for rootkit modification; also includes other scripts to check for deletions
- RootKit Hunter – lightweight security monitoring tool that scans for rootkits and various other threats to LInux systems.
5. Intrusion Detection Software
Intrusion detection software monitors network activity and alerts an administrator when a suspicious event occurs. Some intrusion detection software can immediately react to specific trigger events. These automated responses can help prevent large-scale attacks because of their early reaction times.
Fail2Ban is software that monitors system logs and blocks hackers after multiple failed logins. Beyond Fail2Ban, there are a number of intrusion detection software applications that you may consider. These include:
6. Brute Force Security
Brute force security is used to prevent multiple login attacks in an effort to crack password logins. There are different solutions that can use to help stop brute force attacks including plugins, firewalls, and cPanel’s cPHulk. Fail2ban can also be used to help stop brute force attacks as it monitors logins.
cPHulk
The cPHulk Brute Force Protection application that cPanel provides works at the Pluggable Authentication Module (PAM) level to detect failed login attempts. Once a set number of failed login attempts has been reached, cPHulk will block any further login attempts from the IP address that had been attempting them.
Because cPHulk blocks IPs at the PAM level, it’s safe to blacklist entire blocks of IP addresses such as a certain country, without having to worry about users from those IPs not being able to access your websites or email you. They will simply be denied access to attempt a login to one of the cPanel core services.
Learn more about enabling cPHulk Brute Force Protection through InMotion Hosting.
CSF Login Failure Detection
The ConfigServer Firewall (CSF) can also be used in Brute Force protection by enabling LFD (Login Failure Detection). You can enable the LFD brute force protection by editing:
vi /etc/csf/csf.conf
LF_DAEMON=1
You can use the LF_* settings down further in the file to set the login limits for each service on the server.
7. Use SSH Keys
When you have multiple users logging into the server, one of the best ways to secure login is to use SSH-key authentication. With no password logins, using public and private key pairs ensures a secure login.
SSH keys work by using a public key and a private key. The private key is kept hidden from the user, while the public key is shared with the server where they require access. The keys are matched during login allowing authentication without using a password.
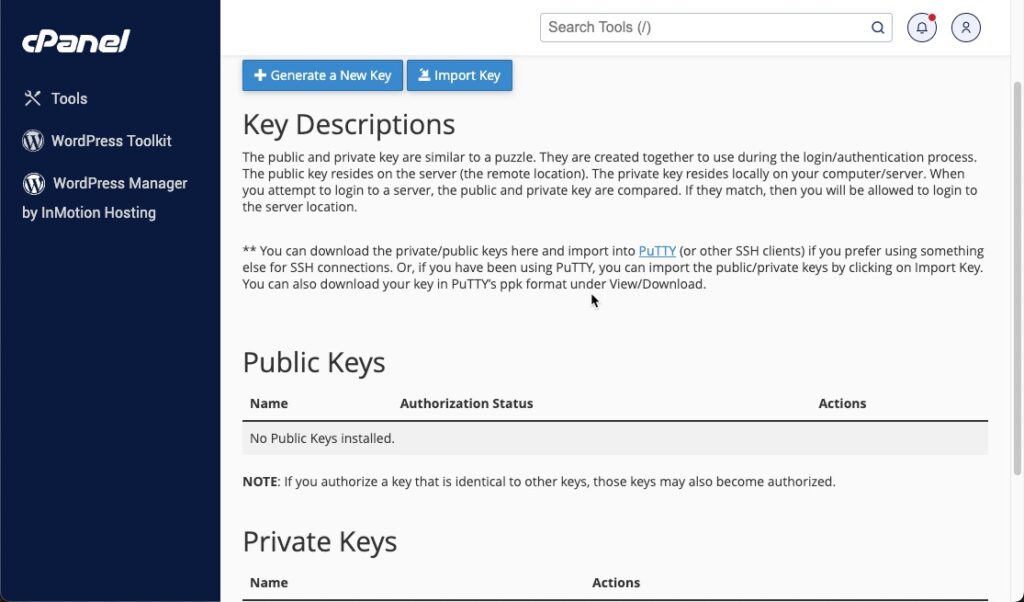
cPanel makes it easy to manage and generate the needed keys. You can see the cPanel interface in the screenshot above.
The complexity of the encryption helps to keep the login safe from brute-force attacks. You can learn how to create the keys in this tutorial: How to Generate SSH Keys.
8. Use SFTP instead of FTP
In the past, file management on your server used to take place via FTP, which stands for File Transfer Protocol. But, we now highly recommend utilizing SFTP instead to better protect and secure your server. Learn why FTP is insecure, why you should use SFTP instead, how to disable FTP on your whole server or for a specific cPanel user, then we’ll show you how to use SFTP.
Keep in mind that InMotion Hosting provides support for SFTP on all of its hosting accounts.
Why is FTP Insecure?
FTP has been around for a very long time and was not designed with modern security practices in mind. With FTP, login credentials use plain text so they are not encrypted, this could possibly be intercepted during transmissions. Another issue is the data or commands you send and receive from your server could be exposed.
When enabled, FTP servers can be a target of distributed denial-of-service attack (DDoS) attacks. This can negatively affect the overall performance of your entire server.
Also, you should never enable anonymous FTP logins since it would allow anyone to upload/download files from your server, which is a huge security risk.
Why Use SFTP?
SFTP, short for SSH FTP or Secure FTP normally uses a user and password login and can be accessed through SSH, an FTP Client (such as FileZilla), or with the FTP interface provided by the server software.
To help provide better security, your servers will block all users by default. Users are only able to connect after their IP address has been whitelisted. This means that only the specific machines that are added to an “allow” list will be able to connect and communicate with the server. All other users will be blocked.
How to Disable FTP On the Server
- Login to WHM.
- Search for FTP, then select the FTP Server Selection option in the Service Configuration section.
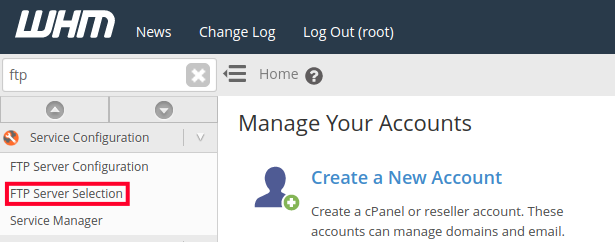
- Set the FTP Server option to Disabled.
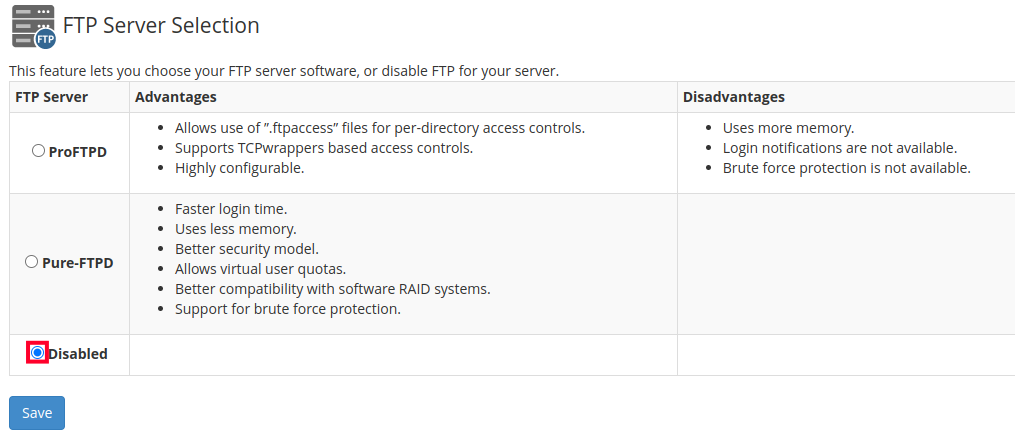
- Click the Save button.
How to Disable FTP For Specific cPanel Users
Since all cPanel users automatically are able to connect using FTP, you should also consider disabling access for each user. This would ensure they are only able to connect via SFTP.
- Connect to your server via SSH, as the root user.
- Edit the /etc/ftpusers file. If it’s not there already, you can create it with the following command.
nano /etc/ftpusers
- List each user that you want to block on a separate line, for example:
joeuser01
joeuser02
joeuser03
joeuser04 - Save your changes by clicking Ctrl+O then the Enter key.
- You can then verify the user was disabled by attempting to connect via FTP. In my test I received the following message:
Critical error: Could not connect to server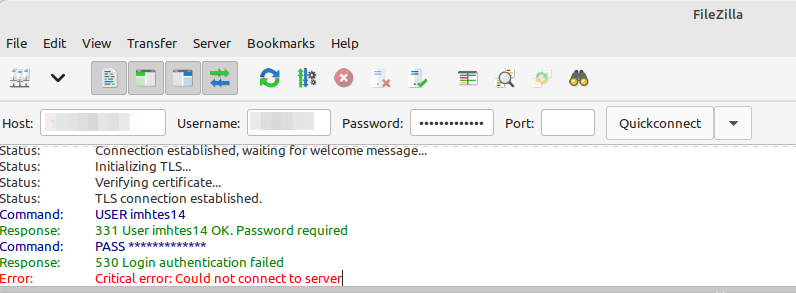
How to Connect Using SFTP
- Identify the IP address of the computer you want to connect from.
- Add the IP address to the server’s firewall.
- Finally, you can connect using an SFTP client such as FileZilla, WinSCP, or Cyberduck. Below are the default SFTP settings, for more detailed information, see our full guide on how to Connect with SFTP.
You can also learn more about SSH security and SFTP if you are using the Ubuntu Cloud Server.
9. Spam Filtering
Spam filtering is very important as it helps prevent a vector for malware from making it to your server or users. It also will help keep the email server working through thousands of unnecessary emails that may be slowing your server down.
InMotion Hosting provides cPanel hosting that includes Spam Filters that is powered by SpamAssassin. To learn more, check our articles on SpamAssassin: Fighting Spam.
10. Disable IPV6
IPv6 was created because IP addresses in the IPv4 system were running out. However, most people are still only using iPv4.
Currently, the use of iPv6 can make your server vulnerable to attacks.
Though your hosting service may support IPv6, it is currently recommended that it be disabled to help shut down a possible avenue of malicious traffic to your site.
Inquire with your hosting service if they are supporting IPv6 and if they are planning to adapt it if they are not. If you are not familiar with disabling IPv6 you can request that they help with this request. If you wish to do it yourself, you will need to log into your server and run the following commands with root privileges.
- Use an editor to edit the sysctl.conf file. It is located here: /etc/sysctl.conf
- Add the following two lines:
net.ipv6.conf.all.disable_ipv6=1
net.ipv6.conf.default.disable_ipv6=1 - Next, run the following command to use those settings:
sysctl -p
You can find more information in the cPanel documentation to disable IPv6.
11. Disable Root Logins
Another way to harden VPS security is to disable Root access. Root access logins give you complete access to the server. As the default user is “root”, it makes the system vulnerable to brute force attacks that try to gain access to the account.
You can create a new username and then use the “sudo” command to execute root-level commands.
Make sure that you create your new admin account with the appropriate access levels before disabling the root account.
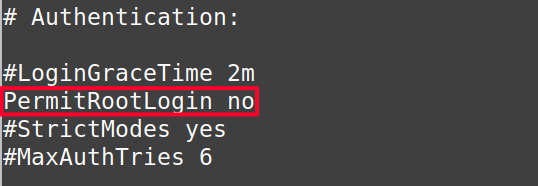
You will need to have root access before changing the PermitRootLogin parameter in the sshd_config file. Changing the value to “No” will prevent the “root” user from being used to log in to the server.
Note: You can request root access to InMotion Hosting VPS accounts, but it is not provided by default.
Disabling root Logins
Before you begin, you should choose an existing cPanel account user that you want to elevate access for, or you can create a new cPanel account that will include a new user. This user will essentially “replace” the root user.
- Login to WHM.
- Search for ‘wheel’ then click the Manage Wheel Group Users option under Security Center.
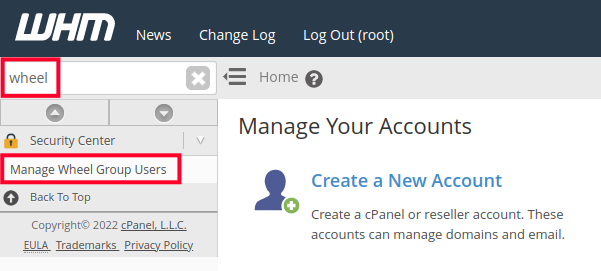
- Under the section labeled “Add a user to the wheel group” select the user you want to use for root access and click the Add to Group button. You will then see a message stating that the user was added to the wheel group.

- Connect to your server via ssh with the new wheel user. For example:
ssh [email protected]
- Run the su command and enter your root password to change to the root user.
su
You should then see root@ listed in your terminal.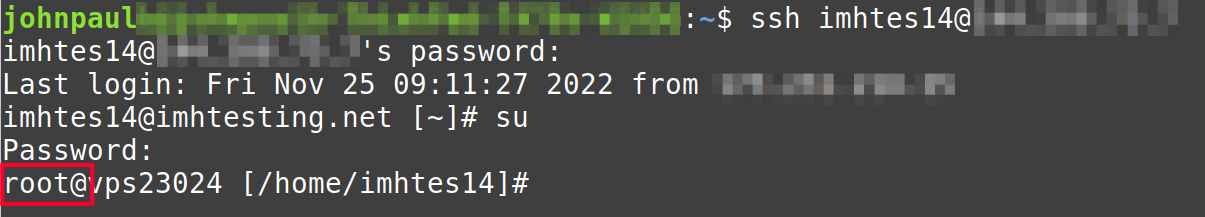
- We will now edit the sshd_config file to disable the root user. In this example, I’m using the nano command but you can use any editor that you prefer.
nano /etc/ssh/sshd_config
- Locate the following line in the file:
#PermitRootLogin yes
Remove the hashtag ‘#’ in the line and change yes to no. It should then look like this:PermitRootLogin no
- Save your changes. If you are using nano it will be Ctrl+x, the y key, then Enter.
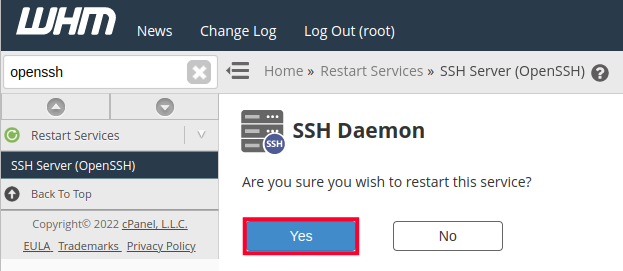
- We will now restart ssh by logging into WHM and searching for ‘openssh’ then clicking the SSH Server (OpenSSH) link under Restart Service.
- Click the Yes button on the SSH Daemon page.
12. Limit User Access – Review and Manage users
In many cases, a server is accessed by multiple users. This requires that you monitor and manage the users who have access. You should regularly review the users who have access to the server.
Monitoring Users
To view a list of users through SSH, use the following command
getent /etc/passwdThis will display all users, including those authenticated through LDAP. If you are not using LDAP, then you can list all users using LESS to display the passwd file page by page.
less /etc/passwdMonitoring user activity in Linux will require the use of accounting utilities. These utilities are included in the psacct or acct package. You will need to install these packages and start the service. RPM-based Linux systems use psacct.
- Use this command to install the accounting utilities. Note that some variations of Linux may have different installation commands.
sudo apt install acct - When the installation is complete, use this command to enable it.
sudo systemctl enable acct - You will then need to start the service like this:
sudo systemctl start acct - Once the service is started, check its status with this command:
sudo systemctl status acct
The options in the accounting utilities allow you to retrieve activities as stored by the root user. This includes all users in the installation. So, even if users clear their command line history, the records will still exist since they are saved with the root user.
The accounting utilities include the following options to monitor user activity:
- ac user– Displays statistics on specific user login time
- lastcomm user – displays info on executed commands of a particular user
- as -m – displays the number of processes and CPU minutes per user
- dump-acct – transforms the output file to a human-readable format
Use the man page for the commands to see all of their options.
When you are reviewing your users, check the following:
- The frequency of their access. Are they accessing the server excessively? Do they rarely access the server? If necessary, adjust their user rights or expiration dates.
- Resource usage by users. You can identify the users that use higher levels of resources and then determine if changes are needed.
- The validity of their access. Review what commands they use to ensure they have the appropriate access and are not abusing the server.
- Current and obsolete users. Remove users who no longer need access to the server.
Managing Users
The typical commands for managing users using SSH in Linux are useradd, usermod, and userdel. You will also find user account information in the /etc/passwd file. To add security to the password hashes in the /etc/passwd file, the /etc/shadow file was created. The /etc/shadow file is only readable by root.
The /etc/shadow file contains the username, a hashed version of the password, the password change period, and the user’s status.
Examples of the useradd, usermod, and userdel commands:
Useradd is used to add users.
sudo useradd usernameUsermod modifies users.
sudo usermod -l new-user-name old-user-nameUserdel removes users.
sudo userdel -f usernameEach command has many options best seen on the corresponding man page.
Password Expirations
You can also set expiration dates on users and passwords with specific commands. To view a user’s expiration date, use the following command:
chage -l usernameThe output will appear like this:
Last pasword change : Feb 5, 2023 Password expires : never Password inactive : never Account expires : never Minimum number of days between password change : -1 Maximum number of days between password change : -1 Number of days of warning before password expires : -1
To change the expiration date:
usermod -E 2023-02-28 usernameYou can then repeat the chage command again to verify the change in the user expiration date.
The period of time between password changes can also be set with the chage command. You can set the maximum number of days a password is valid, the minimum number of days between password changes, and the number of days of warning before a password change is required.
This is an example of setting the max days for the password for an account.
chage -M 30 usernameThis command sets the maximum number of days between a required password change. If you were to look at the aging information using chage -l, and it would look like this:
Last pasword change : Feb 5, 2023 Password expires : never Password inactive : never Account expires : never Minimum number of days between password change : -1 Maximum number of days between password change : 30 Number of days of warning before password expires : -1
There are many command options, but the minimum and warning options are detailed below:
| chage -m | Set the minimum number of days between password changes. If the value is “0” then the user may change the password at any time. |
| chage -W | Set the number of days of warning before a password change is required. |
13. Set up a Disaster Recovery Plan – Backups
Creating a disaster recovery plan involves your IT person or personnel responsible for the maintenance of your server. First, you will need to make sure that you are maintaining current and secure backups of your work.
Your plan should take into account intrusion or loss of personnel and loss of services. You should have secure documents that allow you to recover your data and/or logins. If you can restore your services on a different host, then you will be able to recover your data and operations with minimal fuss.
Backups should follow the 3/2/1 rule to prevent data loss:
(3) Three copies of data stored on…
(2) Two different types of media (e.g., remote server and local external drive) with
(1) One complete server backup stored off-site in a remote location (especially important in the case of natural disasters that might affect your hosting server)
Your backup process should be automated and reviewed on a regular basis. What is your website and data worth to you? Chances are, it’s priceless. Verify the integrity of your backups and make sure they are in a secure area.
How To Schedule Automatic Backups
With a VPS you have the ability to enable and schedule automatic backups for your cPanel accounts. Below are the basic steps, but we recommend our full guide on Scheduling cPanel Backups in WHM for more detailed information.
- Login to WHM as the root user.
- Click the Backup Configuration option in the Backup section.
- Select the Enable option in the Backup Status section.
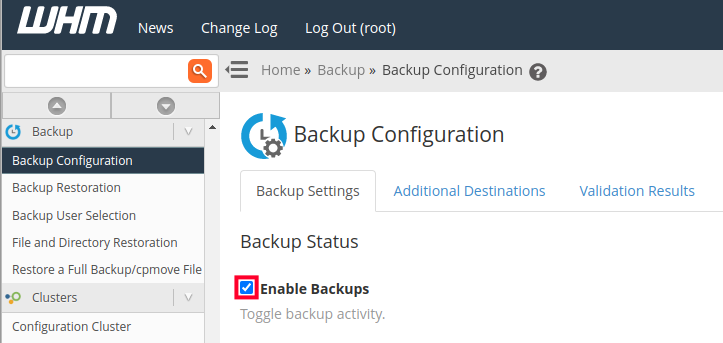
- You can then choose your backup settings. Specifically, you can select the Daily, Weekly, or Monthly backups in the Scheduling and Retention section.
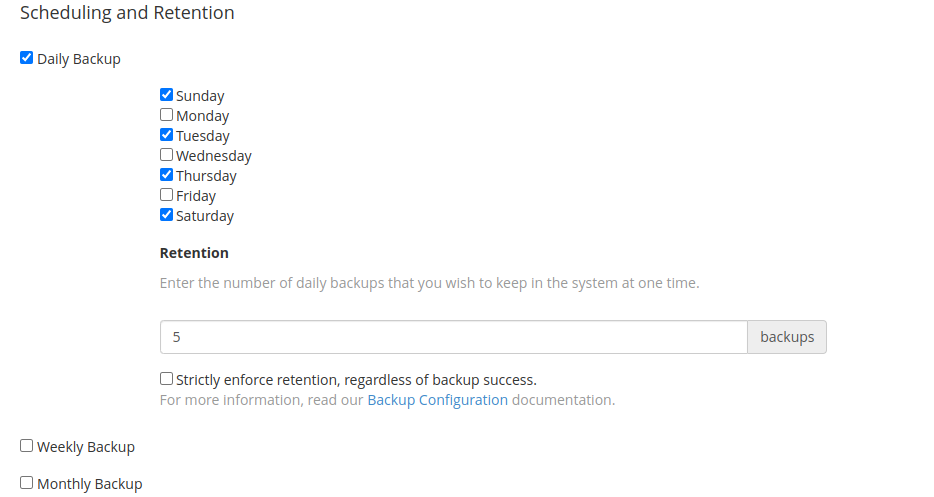
- Click the Save Configuration button.
14. Keep Everything Up-to-date
Keeping all the software “up-to-date” may seem like common sense but it may be more complex than you think. As an administrator, you should keep track of all the software and applications that require manual updates as well as the ones that automatically update.
Additionally, it is equally important to track software that does not update, especially over long periods of time. Software that doesn’t regularly update could become vulnerable to security issues. Additionally, it may cause conflicts as your other systems are updated.
For example, you may have plugins on your website that do not get updated. But when the CMS software updates, your plugin may no longer operate correctly.
While keeping track of all the software and applications that you run on your VPS may be a minor nightmare, it is more important that you have an understanding of what software you are using and make sure that is kept up-to-date in order to keep things safe and secure.
15. Monitor Server Logs
Monitoring your website is another key step in the effort to harden VPS security. You can monitor website logs that include traffic, resources, and errors.
You can also watch logs for the server that include the server load, resource usage (CPU, memory, bandwidth, etc.), email logs, and web server logs. This will keep you informed about the health and load on the server.
Regular monitoring will help you to establish a baseline as to how your server normally performs versus when it’s operating under a heavy load or with no load at all. cPanel provides a number of logs that can help you with that specific cPanel account.
To see a list of logs from cPanel see cPanel logs: Access, Apache, Email, Error, FTP, MySQL, and WHM.
16. Implement a Strong Password Policy
A strong password policy means that all personnel is required to use a password that meets the set security standards. Having a strong password is important for dedicated server security and any other hosting account too.
Password length of 8 characters or more, with at least 1 capitalized letter, a number, and a special character is a decent standard for security. Enforcement of this policy should be automated so that everyone must take part in it.
Learn more in our article Password Strength and Security.
17. PCI DSS Compliance
Many businesses require that servers by Payment Card Industry Data Security Standard (PCI DSS) compliant. This allows for a secure setting for online store payments. PCI compliance requires many of the security options that we have discussed in this article. They include:
- Current firewall configuration
- Antivirus Software
- Network monitoring
- Regular Security Testing
- Unique IDs and strong passwords
- Cardholder data encryption on public networks
To learn more about PCI Security standards, go to their website: PCI Security Standards.org.
18. Use SSL Certificates
SSL certificates are important in providing a secure connection between your web server and your visitor. It is important to have an SSL certificate that matches the needs of your website and business.
While there are free SSL certificates there are also many types of paid SSL certificates that can provide further authentication for your website. For instance, an Extended Validation SSL Certificate would authenticate not only the owner of the domain but also the validity of the business that claims to be the owner of the website. Although the encryption works the same way, this added layer of validation can help your visitors trust your website and business as one entity.
If you are moving your website to a new location always keep in mind that the SSL certificate may be part of the migration. In some cases, it may require assistance from your new host, but it should be considered a required step for your business site.
19. Security HTTP Headers and Subresource Integrity (SRI)
HTTP Security headers are exchanged between a browser (or web client) and a server in order to authenticate the HTTP communication. There are many types of HTTP headers, but we’ll list a few and describe them:
- X-Frame-Options HTTP Header – security header used to avoid UI Redressing attacks that started with Clickjacking. It is supported by all major browsers
- Content-Security-Policy (CSP) – security header used to protect the website and visitors from cross-site scripting (XSS) attacks as well as data injection attacks.
- HTTP Strict-Transport-Security (HSTS) – tells browsers that the website can only be accessed using HTTPS.
- X-Content-Type-Options – used by the server to indicate that MIME types listed in the Content-Type headers should be used and not changed. Used to avoid Mime sniffing. Mime sniffing is generally a precursor to XSS attacks because it can change the way the browser interprets an asset file making it vulnerable to a different file type that can be used to transport the malware code.
- HTTP headers also control browser feature settings, cookie storage, and much more. There are also plugins for CMS software like Joomla and WordPress that can provide HTTP header security.
Subresource Integrity (SRI) is a security feature that lets browsers authenticate that the server they’re getting data/media from is being sent without being manipulated by an unexpected source. SRI works by using encrypted hashes that must be matched by the resource from where you are receiving your media.
20. PHP Versioning
PHP is often the backbone of website software and applications used on VPS servers. New versions of the software are often released that provide improved performance and security for the applications that use it. Regularly keeping your PHP versions up-to-date should be a required step in your efforts to harden VPS security.
PHP versions may often require installation through the backend of the server. For example, in CENTOS, new versions of PHP are normally installed through EasyApache.
Depending on your host, some versions may not be immediately available. However, it is important to inquire with your technical support team in order to understand when new versions become available so that you can install them on your server.
21. Disk Partitioning
Disk partitioning is used on servers and computers to define spaces on a hard drive that can be assigned a logical space. For example, you can dive a drive into two separate spaces – c: and d:.
These partitions can then be used to separate the operating system and applications on the root hard drive. Keeping the executable applications separate from your data works to harden VPS security because the written or created data can be protected from malware affecting the application.
This allows you to restore or reload software applications or operating systems without actually affecting your data that can be saved in a different partition. It also helps to keep your backups to a manageable size, since your backups can be limited to only the data that needs to be saved.
22. Specific Security for your Operating System
You may have software that has built-in security options depending on the software loaded to your server. This could be the operating system for the server or CMS software used to build your website. There are many built-in or add-on options that work to harden your VPS security.
cPanel Security Options
cPanel is server software that also provides the WHM software that gives your a graphic interface to manage the server. cPanel includes many security options including a Security Advisor in WHM that offers recommendations for your password policy, databases, SSH, email, and more.
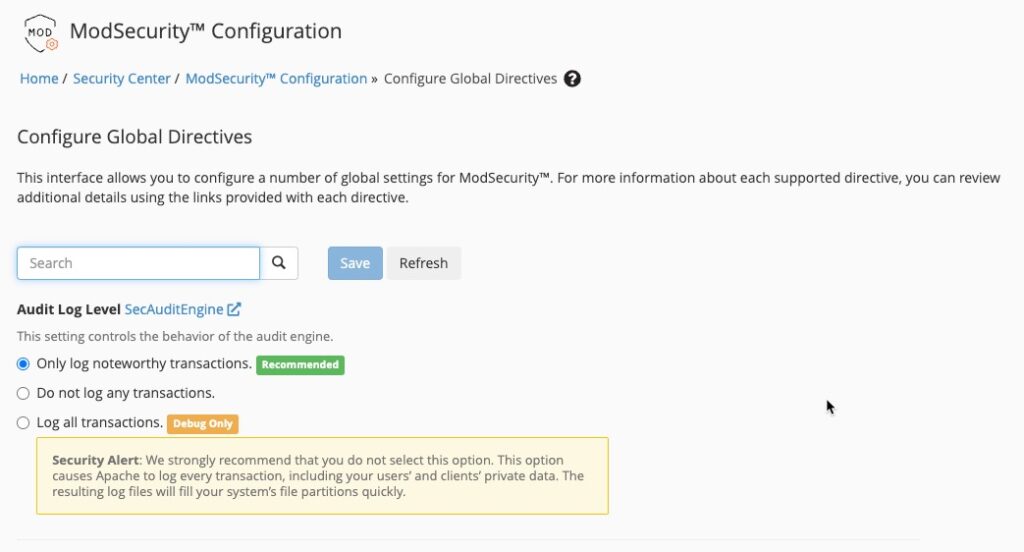
ModSecurity is an open-source web application firewall. It allows you to set up rules that can setup real-time monitoring and logging. It can also be used to filter HTTP traffic. The ModSecurity engine is deployed inside a web server so that it can monitor incoming and outgoing HTTP traffic. To learn more about using ModSecurity, check out the Apache Module: ModSecurity.
CMS Security Options
CMS security options will vary from CMS to CMS. Active and popular ones like
WordPress has a variety of options that you can implement. Typically, these security
options will be plugins. But there are also services that can be hired that will help
monitor your website to keep it safe and secure.
Some examples of security plugins for WordPress include:
- iThemes Security – stops automated attacks, monitors suspicious activity, scans for vulnerable plugins and themes, blocks bad bots, reduces spam, strengthens user credentials
- WordFence Security – provides login security, centralized management, two-factor authentication, malware scan, firewall, and a 24/7 Incident Response Team
- Bullet Proof Security – plugin provides malware scanner, login monitoring and security, security logging, error logging, hidden plugin folders, backups
Sucuri Security – both a security plugin and also a paid service; provides malware and hack removals, firewall, security scans, blocklist monitoring and removal, SSL support and monitoring, and CDN services
23. Training and Research VPS Security
Working in security and researching security for your VPS server will be a never-ending task. However, securing your server from attacks is rewarding because it protects your business and the privacy and data of your clients.
Training for security can lead to certifications and degrees and will require some imagination as the attacks on your server can come from various directions.
Annual conferences like Black Hat, Open Security Summit, and Linux Foundation events show that security is continually evolving in order to meet the threats and changes to the industry and the world around us.
24. Find a Secure VPS Hosting Service
When you’re looking for a host for a VPS server, make sure to check out their reputation by reading reviews about their service and security.
If you don’t have much information, make sure to ask them questions about their policies and experiences when working to harden VPS security and technical support.
The information you should be seeking when looking for a good secure VPS hosting provider includes:
- Server location
- Power outage mitigation measures at the data center
- Physical security at the data center
- Onsite support for physical server maintenance
- Network monitoring
- Backups for your data and applications
- DDoS Prevention
- Backup network plans in the event of a service outage
Enjoy high-performance, lightning-fast servers with increased security and maximum up-time with our Secure VPS Hosting!
Linux VPS
cPanel or Control Web Panel
Scalable
Website Migration Assistance
Managed Hosting vs Unmanaged Hosting
Managed hosting is more secure as it normally involves a team of people actively monitoring the server. They will also help to keep the server software up-to-date.
An “unmanaged” server will often be one where it will be up to your to load security software and maintain monitoring. Unmanaged servers may offer more freedom but, they will also be harder to keep secure.
Learning how to secure VPS security is a daunting and never-ending task. However, the price of security for your customers or visitors cannot be understated. This list of 24 recommendations will help guide you toward the goal of securing your VPS, but it is important to keep in mind that you are not the only person involved in the task. Your users, administrators, and even the tech support team from your hosting server all play an important role in keeping your data and applications safe and secure.
